Scan To PDF
Scan your files using AI and remove the background.Trusted by
No Login Required to Try!Preview
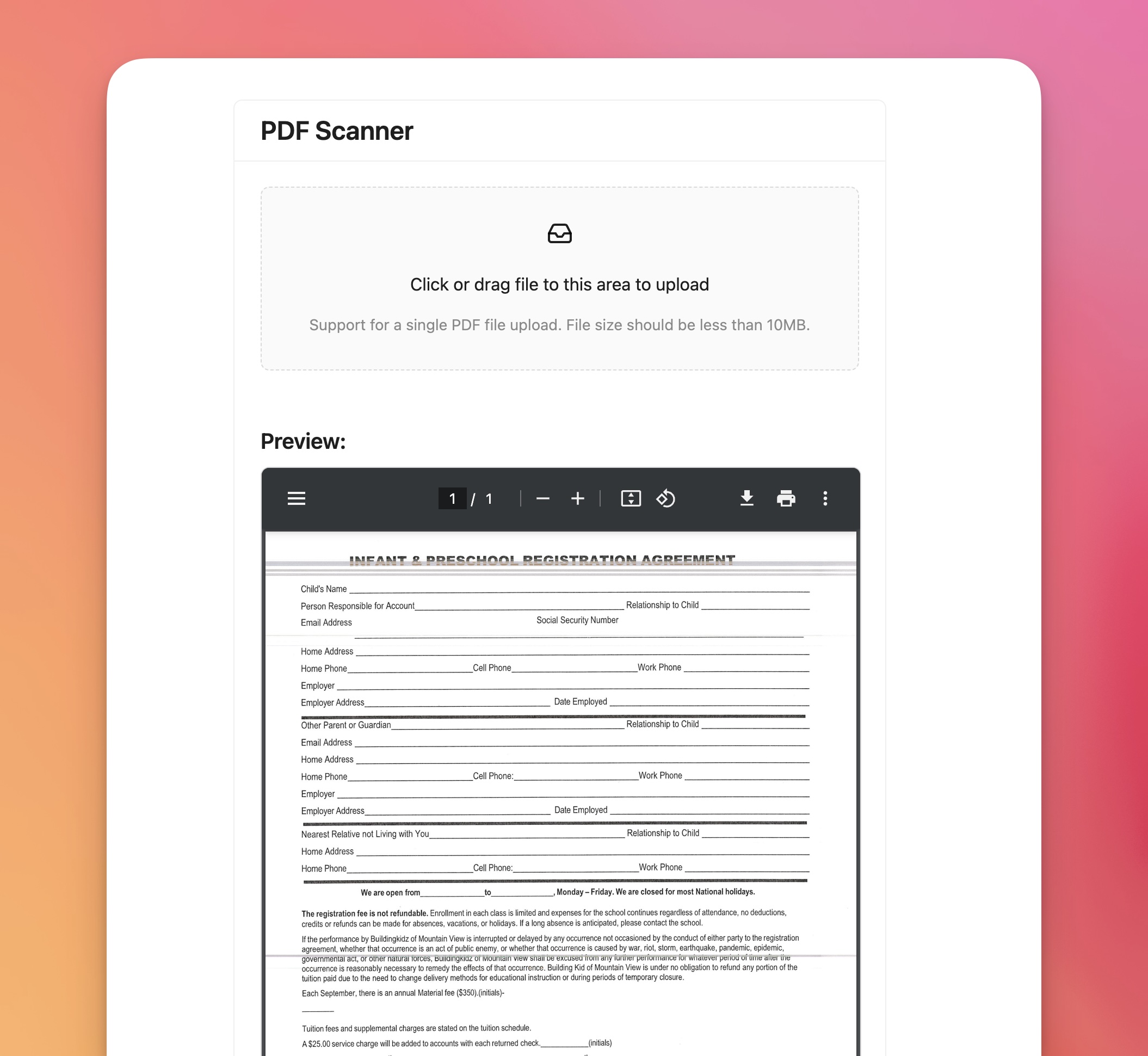
PDF Scanner
Click or drag file to this area to upload
Support for a single PDF file upload. File size should be less than 10MB.
# Introduction to Scan Login: Enhancing Security and User Experience
The digital landscape is continually evolving, and so are the methods we use to gain access to our online accounts. Traditional usernames and passwords are increasingly giving way to more innovative and secure methods of authentication. One such method that is gaining traction is **Scan Login**. In this article, we will delve into what Scan Login is, its benefits, the technology behind it, and how you can implement it for a secure and seamless login experience.
## What is Scan Login?
**Scan Login** is a form of authentication that allows users to log into their accounts by scanning a QR code or using biometric data such as fingerprint or facial recognition. This approach leverages the capabilities of modern smartphones and biometric sensors to provide a secure and user-friendly login process.
## Benefits of Scan Login
### 1. Enhanced Security
Scan Login significantly reduces the risk of unauthorized access. Unlike traditional passwords that can be stolen or guessed, biometrics and QR codes are much harder to replicate. Even if a QR code is intercepted, it is typically valid for only a short period, minimizing the risk of misuse.
### 2. Convenience
Gone are the days of remembering complex passwords. With Scan Login, users can quickly access their accounts using their smartphones or biometric data, making the login process faster and more convenient.
### 3. Reduced Password Fatigue
Frequent password changes and the need to remember multiple passwords can lead to password fatigue. Scan Login simplifies the user experience, leading to fewer password resets and higher user satisfaction.
### 4. Multi-Factor Authentication (MFA)
Scan Login can serve as an additional layer of security in a Multi-Factor Authentication (MFA) setup. For example, users might need to scan a QR code and then confirm their identity using biometrics, providing a robust defense against security breaches.
## How Scan Login Works
### QR Code Authentication
1. **Generate QR Code**: When a user attempts to log in, a unique QR code is generated and displayed on the login screen.
2. **Scan with Smartphone**: The user scans the QR code using a dedicated authentication app or camera application on their smartphone.
3. **Data Transmission**: The scanned code is decoded, and the app communicates with the server to verify the user's credentials.
4. **Access Granted**: Upon successful verification, the user is granted access to their account.
### Biometric Authentication
1. **Fingerprint/Facial Recognition**: Users can authenticate themselves using fingerprint sensors or facial recognition technology on their devices.
2. **Device Communication**: The biometric data is securely transmitted to the server for verification.
3. **Access Granted**: Once the data is verified, the user gains access to their account.
## Implementing Scan Login
### Step-by-Step Guide
#### 1. Choose a Reliable Authentication Service
Before implementing Scan Login, select a reliable authentication service that supports QR code and biometric authentication. Some popular options include **Authy**, **Google Authenticator**, and **Microsoft Authenticator**.
#### 2. Integrate QR Code Generation
Implement QR code generation in your login interface. This can be achieved using various libraries and APIs, such as **Google Charts**, **QR Code Generator API**, or **JavaScript QR Code Library**.
#### 3. Develop Mobile App Support
Ensure your mobile app or web application supports QR code scanning and biometric authentication. This may involve utilizing SDKs like **Firebase**, **Twilio Authy**, or **Okta** for seamless integration.
#### 4. Implement Secure Communication
Ensure that all communication between the user's device and your server is encrypted using **SSL/TLS** protocols. This prevents interception and unauthorized access to sensitive data during transmission.
#### 5. Test Thoroughly
Conduct extensive testing to ensure the Scan Login process is seamless and secure. Address any potential vulnerabilities and optimize the user experience.
## Best Practices for Scan Login
### 1. Educate Users
Provide clear instructions and educational materials to help users understand how to use Scan Login effectively and securely.
### 2. Regular Updates
Regularly update your authentication system and mobile app to incorporate the latest security features and improvements.
### 3. Monitor Activity
Continuously monitor login activity for any signs of suspicious behavior and be prepared to implement additional security measures if necessary.
### 4. Backup Options
Offer alternative login methods for users who may not have access to a smartphone or biometric sensors, ensuring inclusivity and accessibility.
## Conclusion: Embrace the Future of Secure Login with Scan Login
Scan Login is revolutionizing how we authenticate our online presence, offering a more secure and user-friendly alternative to traditional passwords. By leveraging QR codes and biometric technology, Scan Login enhances security, convenience, and user satisfaction.
Implementing Scan Login not only protects sensitive data but also streamlines the login process for a seamless user experience. As security threats continue to evolve, adopting advanced authentication methods like Scan Login is an essential step towards safeguarding digital identities.
Feel free to share your thoughts and experiences with Scan Login in the comments below. If you found this article helpful, consider sharing it with others to spread the knowledge. Stay secure and embrace the future of digital authentication!
---
Remember to subscribe to our blog for more articles on the latest advancements in technology and security.
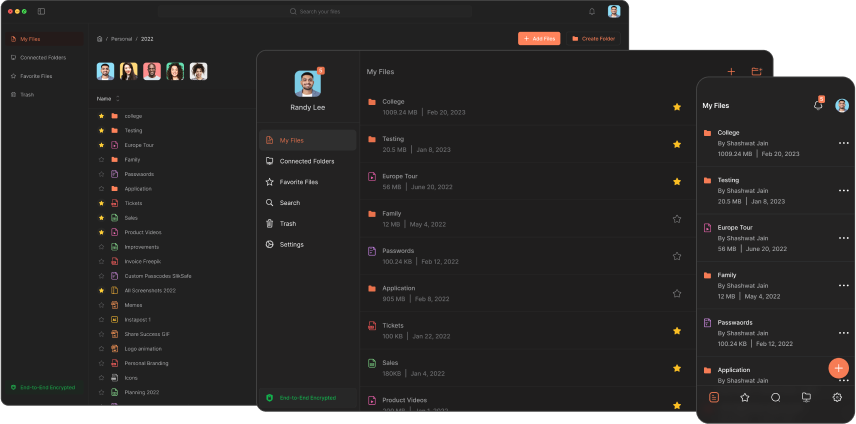
Download Now
The Slikest Files Experience Ever Made
CompanyBlogsCareersFAQsAbout Us
ProductPricingDownload
SupportContact Us
LegalTerms of ServicePrivacy PolicySecurity
ToolsAll ToolsGetting StartedTips & TricksGenerative AIThe Future of AIDocument ManagementSecurityFAQs
BooksBook SummaryThe AlchemistWe'll Always Have Summer
Rainbow Labs Inc. | Copyright 2025 | v0.9.61